https://github.com/authelia/authelia
The Single Sign-On Multi-Factor portal for web apps
https://github.com/authelia/authelia
2fa authentication docker golang kubernetes ldap mfa multifactor oauth2 openid-connect passkeys push-notifications security sso sso-authentication totp two-factor two-factor-authentication webauthn yubikey
Last synced: 3 months ago
JSON representation
The Single Sign-On Multi-Factor portal for web apps
- Host: GitHub
- URL: https://github.com/authelia/authelia
- Owner: authelia
- License: apache-2.0
- Created: 2016-12-07T00:56:57.000Z (over 9 years ago)
- Default Branch: master
- Last Pushed: 2025-05-05T05:42:30.000Z (about 1 year ago)
- Last Synced: 2025-05-05T11:16:32.239Z (about 1 year ago)
- Topics: 2fa, authentication, docker, golang, kubernetes, ldap, mfa, multifactor, oauth2, openid-connect, passkeys, push-notifications, security, sso, sso-authentication, totp, two-factor, two-factor-authentication, webauthn, yubikey
- Language: Go
- Homepage: https://www.authelia.com
- Size: 57.2 MB
- Stars: 23,637
- Watchers: 162
- Forks: 1,209
- Open Issues: 83
-
Metadata Files:
- Readme: README.md
- Contributing: CONTRIBUTING.md
- Funding: .github/FUNDING.yml
- License: LICENSE
- Code of conduct: CODE_OF_CONDUCT.md
- Security: SECURITY.md
Awesome Lists containing this project
- awesome-go - authelia/authelia - On Multi-Factor portal for web apps|16,298| (Popular)
- awesome-tools - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps (Authentication)
- awesome-auth - Authelia - The Single Sign-On Multi-Factor portal for web apps. (SSO (Single-Sign-On), IAM (Identity Access Management))
- awesome-starred - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps (golang)
- definitive-opensource - authelia - On Multi-Factor portal for web apps, now OpenID Certified™ | `SelfHost` | **27.8k** | (Table of Contents / Authentication)
- StarryDivineSky - authelia/authelia
- awesome-webtech - Authelia - On Multi-Factor portal for web apps. (Applications / General)
- awesome-technostructure - authelia/authelia - On Multi-Factor portal for web apps ([🎛️ yunohost](https://github.com/stars/ketsapiwiq/lists/yunohost))
- awesome-selfhost-docker - Authelia
- cybersecurity-auth - Authelia - The Single Sign-On Multi-Factor portal for web apps. (`Authentication` / `SSO (Single-Sign-On)`)
- stars - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps (Go)
- awesome-rainmana - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps, now OpenID Certified™ (Go)
- awesome-iam - Authelia - 🆓 Open-source authentication and authorization server providing two-factor authentication and single sign-on (SSO) for your applications via a web portal. (Multi-factor auth / Identifiers)
- awesome-starred - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps, now OpenID Certified™ (Go)
- awesome - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps, now OpenID Certified™ (Go)
- awesome - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps, now OpenID Certified™ (Go)
- awesome - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps, now OpenID Certified™ (Go)
- jimsghstars - authelia/authelia - The Single Sign-On Multi-Factor portal for web apps (Go)
- awesome-github-projects - authelia - The Single Sign-On Multi-Factor portal for web apps, now OpenID Certified™ ⭐27,797 `Go` 🔥 (🔒 Security & Privacy)
README

[](https://buildkite.com/authelia/authelia)
[](https://bestpractices.coreinfrastructure.org/projects/7128)
[](https://scorecard.dev/viewer/?uri=github.com/authelia/authelia)
[](https://slsa.dev)
[](https://goreportcard.com/report/github.com/authelia/authelia/v4)
[](https://github.com/authelia/authelia/releases)
[](https://hub.docker.com/r/authelia/authelia/tags)
[](https://hub.docker.com/r/authelia/authelia/tags)

[](https://aur.archlinux.org/packages/authelia/)
[](https://aur.archlinux.org/packages/authelia-bin/)
[](https://aur.archlinux.org/packages/authelia-git/)
[][Apache 2.0]
[](https://opencollective.com/authelia-sponsors)
[](https://discord.authelia.com)
[](https://matrix.to/#/#support:authelia.com)
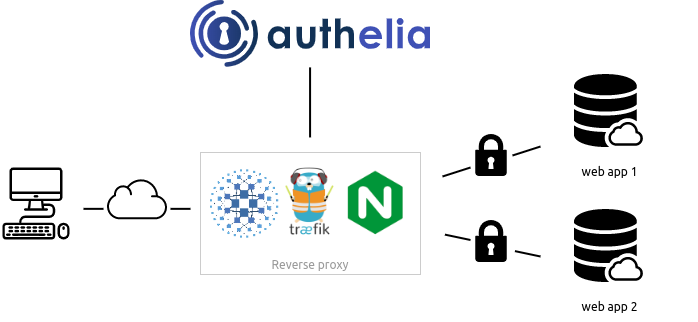
**Authelia** is an open-source authentication and authorization server providing two-factor authentication and single
sign-on (SSO) for your applications via a web portal. It acts as a companion for [reverse proxies](#proxy-support) by
allowing, denying, or redirecting requests.
Documentation is available at [https://www.authelia.com/](https://www.authelia.com/).
The following is a simple diagram of the architecture:
**Authelia** can be installed as a standalone service from the [AUR](https://aur.archlinux.org/packages/authelia/),
[APT](https://apt.authelia.com/stable/debian/packages/authelia/),
[FreeBSD Ports](https://svnweb.freebsd.org/ports/head/www/authelia/), or using a
[static binary](https://github.com/authelia/authelia/releases/latest),
[.deb package](https://github.com/authelia/authelia/releases/latest), as a container on [Docker] or [Kubernetes].
Deployment can be orchestrated via the Helm [Chart](https://charts.authelia.com) (beta) leveraging ingress controllers
and ingress configurations.

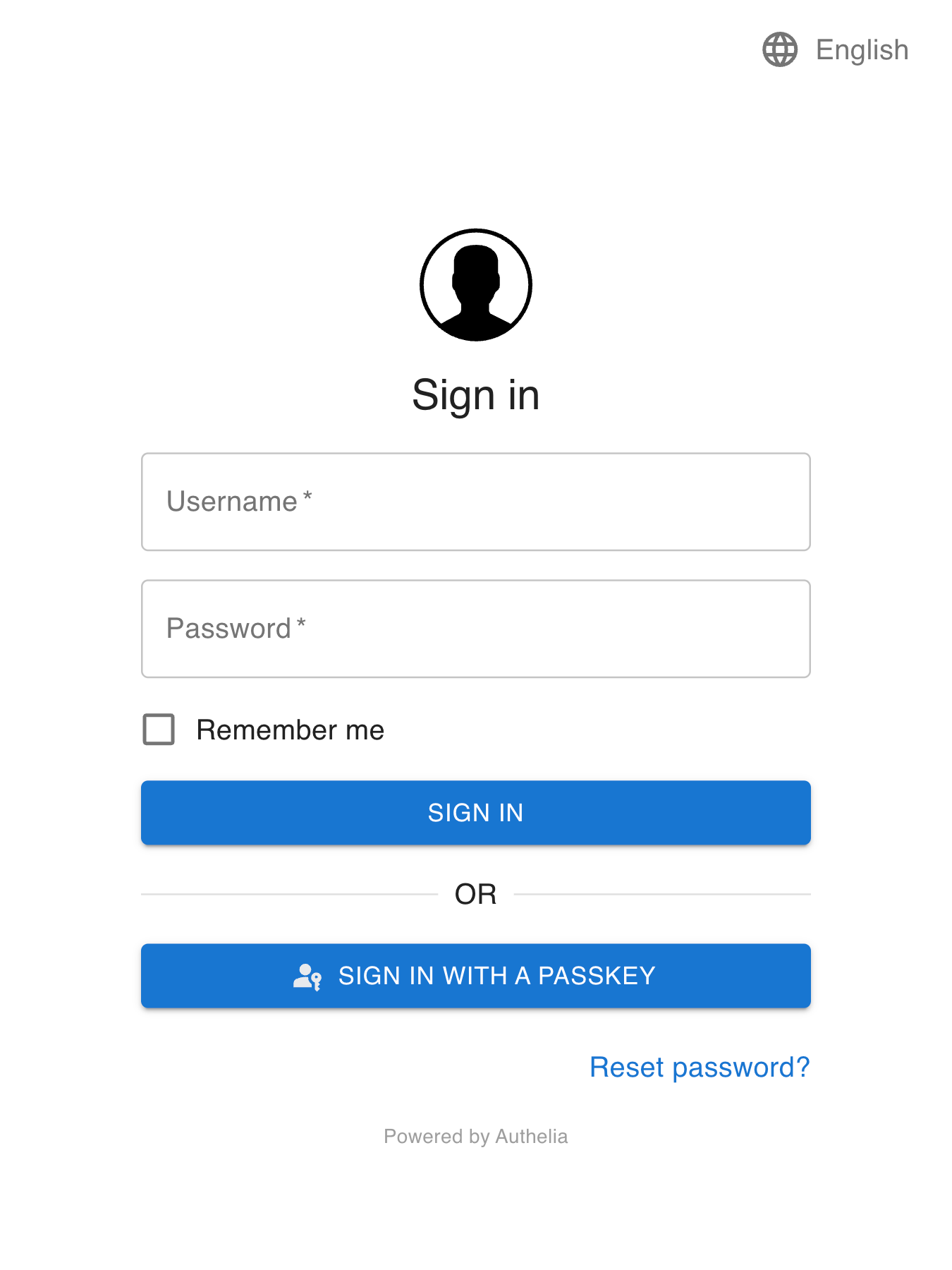
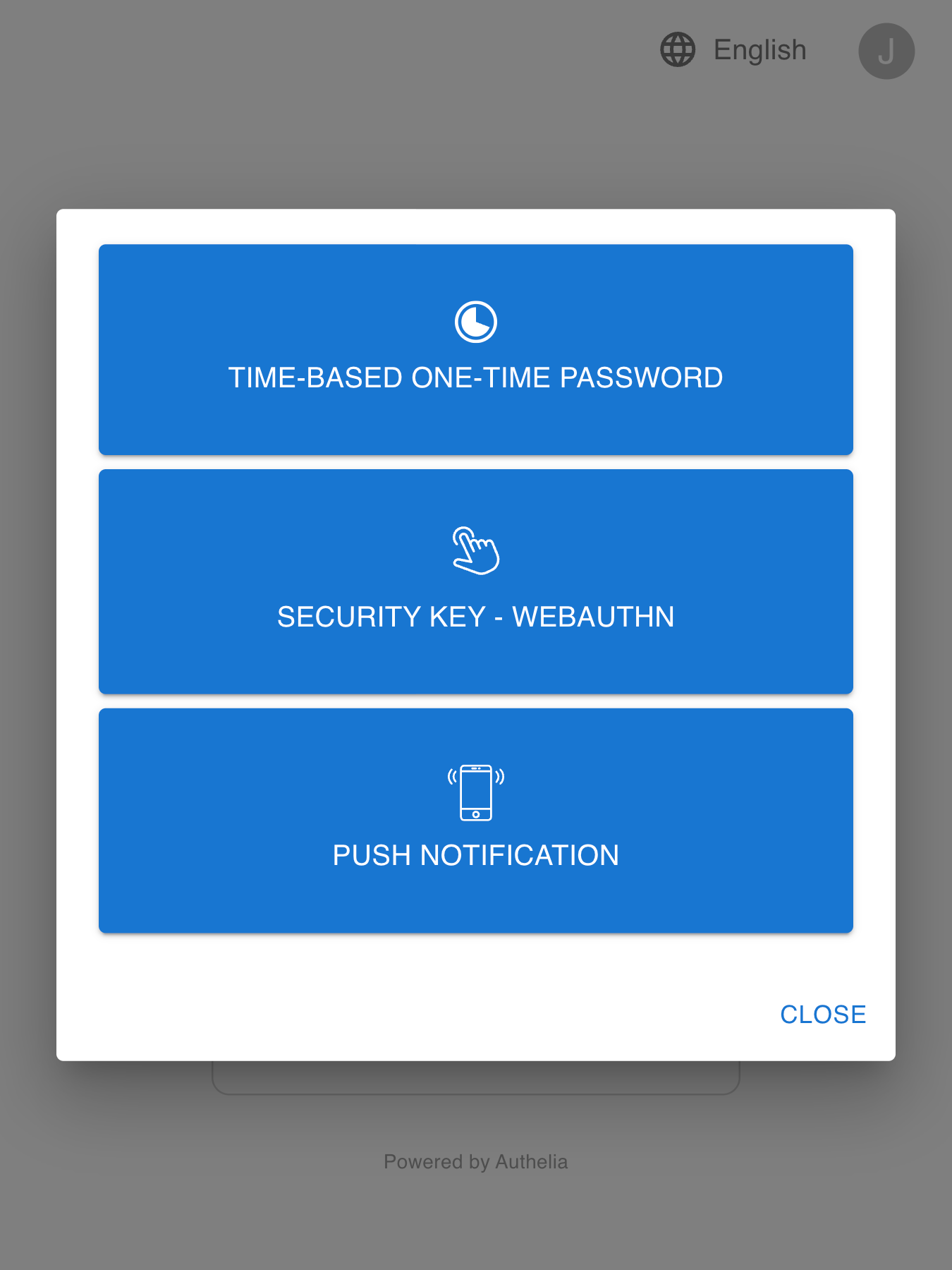
Here is what Authelia's portal looks like:
## Features summary
This is a list of the key features of Authelia:
* [OpenID Connect 1.0 / OAuth 2.0](#openid-connect-10--oauth-20)
* Several second factor methods:
* **[Security Keys](https://www.authelia.com/overview/authentication/security-key/)** that support
[FIDO2] [WebAuthn] with devices like a [YubiKey].
* **[Time-based One-Time password](https://www.authelia.com/overview/authentication/one-time-password/)**
with compatible authenticator applications.
* **[Mobile Push Notifications](https://www.authelia.com/overview/authentication/push-notification/)**
with [Duo](https://duo.com/).
* Passwordless Authentication via WebAuthn (Passkeys)
* Password reset with identity verification using email confirmation.
* Access restriction after too many invalid authentication attempts.
* Fine-grained access control using rules which match criteria like subdomain, user, user group membership, request uri,
request method, and network.
* Choice between one-factor and two-factor policies per-rule.
* Support of basic authentication for endpoints protected by the one-factor policy.
* Highly available using a remote database and Redis as a highly available KV store.
* Compatible with [Traefik](https://doc.traefik.io/traefik) out of the box using the
[ForwardAuth](https://doc.traefik.io/traefik/middlewares/http/forwardauth/) middleware.
* Curated configuration from [LinuxServer](https://www.linuxserver.io/) via their
[SWAG](https://docs.linuxserver.io/general/swag) container as well as a
[guide](https://blog.linuxserver.io/2020/08/26/setting-up-authelia/).
* Compatible with [Caddy] using the [forward_auth](https://caddyserver.com/docs/caddyfile/directives/forward_auth)
directive.
* Kubernetes Support:
* Compatible with several Kubernetes Ingress Controllers and Gateways:
* [ingress-nginx](https://www.authelia.com/integration/kubernetes/nginx-ingress/)
* [Traefik Kubernetes CRD](https://www.authelia.com/integration/kubernetes/traefik-ingress/#ingressroute)
* [Traefik Kubernetes Ingress](https://www.authelia.com/integration/kubernetes/traefik-ingress/#ingress)
* [Istio](https://www.authelia.com/integration/kubernetes/envoy/introduction/)
* [Envoy Gateway](https://www.authelia.com/integration/kubernetes/envoy/gateway/)
* Beta support for installing via Helm using our [Charts](https://charts.authelia.com).
For more details take a look at the [Overview](https://www.authelia.com/overview/prologue/introduction/).
If you want to know more about the roadmap, follow [Roadmap](https://www.authelia.com/roadmap).
### OpenID Connect 1.0 / OAuth 2.0
Authelia is [OpenID Certified™] to the Basic OP / Implicit OP / Hybrid OP / Form Post OP / Config OP profiles of the
[OpenID Connect™ protocol]. While this offering is still effectively
[on the roadmap as a beta](https://www.authelia.com/roadmap/active/openid-connect/) it's very comprehensive and well
implemented already, also allowing us comprehensive certification. Read more about the
[OpenID Certified™] status of Authelia in the
[OpenID Connect 1.0 Integration Guide](https://www.authelia.com/integration/openid-connect/introduction/#openid-certified).
## Proxy support
Authelia works in combination with [nginx], [Traefik], [Caddy], [Skipper], [Envoy], or [HAProxy].




## Getting Started
See the [Get Started Guide](https://www.authelia.com/integration/prologue/get-started/) or one of the curated examples
below.
### docker compose
The `docker compose` bundles act as a starting point for anyone wanting to see Authelia in action. You will have to
customize them to your needs as they come with self-signed certificates.
#### [Local](https://www.authelia.com/integration/deployment/docker/#local)
The Local compose bundle is intended to test Authelia without worrying about configuration.
It's meant to be used for scenarios where the server is not be exposed to the internet.
Domains will be defined in the local hosts file and self-signed certificates will be utilised.
#### [Lite](https://www.authelia.com/integration/deployment/docker/#lite)
The Lite compose bundle is intended for scenarios where the server will be exposed to the internet, domains and DNS will
need to be setup accordingly and certificates will be generated through LetsEncrypt. The Lite element refers to minimal
external dependencies; File based user storage, SQLite based configuration storage. In this configuration, the service
will not scale well.
## Deployment
Now that you have tested **Authelia** and you want to try it out in your own infrastructure,
you can learn how to deploy and use it with [Deployment](https://www.authelia.com/integration/deployment/introduction/).
This guide will show you how to deploy it on bare metal as well as on
[Kubernetes](https://kubernetes.io/).
## Security
Authelia takes security very seriously. If you discover a vulnerability in Authelia, please see our
[Security Policy](https://github.com/authelia/authelia/security/policy).
For more information about [security](https://www.authelia.com/policies/security/) related matters, please read
[the documentation](https://www.authelia.com/policies/security/).
## Contact Options
Several contact options exist for our community, the primary one being [Matrix](#matrix). These are in addition to
[GitHub issues](https://github.com/authelia/authelia/issues) for creating a
[new issue](https://github.com/authelia/authelia/issues/new/choose).
### Matrix
Community members are invited to join the [Matrix Space](https://matrix.to/#/#community:authelia.com) which includes
both the [Support Room](https://matrix.to/#/#support:authelia.com) and the
[Contributing Room](https://matrix.to/#/#contributing:authelia.com).
- The core team members are identified as administrators in the Space and individual Rooms.
- All channels are linked to [Discord](#discord).
### Discord
Community members are invited to join the [Discord Server](https://discord.authelia.com).
- The core team members are identified by the **CORE TEAM** role in Discord.
- The [#support] and [#contributing] channels are linked to [Matrix](#matrix).
### Email
You can contact the core team by email via [team@authelia.com](mailto:team@authelia.com). Please note the
[security@authelia.com](mailto:security@authelia.com) is also available but is strictly reserved for [security] related
matters.
## Breaking changes
Since Authelia is still under active development, it is subject to breaking changes. It's recommended to pin a version
tag instead of using the `latest` tag and reading the [release notes](https://github.com/authelia/authelia/releases)
before upgrading. This is where you will find information about breaking changes and what you should do to overcome
said changes.
## Why Open Source?
You might wonder why Authelia is open source while it adds a great deal of security and user experience to your
infrastructure at zero cost. It is open source because we firmly believe that security should be available for all to
benefit in the face of the battlefield which is the Internet, with near zero effort.
Additionally, keeping the code open source is a way to leave it auditable by anyone who is willing to contribute. This
way, you can be confident that the product remains secure and does not act maliciously.
It's important to keep in mind Authelia is not directly exposed on the
Internet (your reverse proxies are) however, it's still the control plane for your internal security so take care of it!
## Contribute
If you want to contribute to Authelia, please read our [contribution guidelines](CONTRIBUTING.md).
Authelia exists thanks to all the people who contribute so don't be shy, come chat with us on either [Matrix](#matrix)
or [Discord](#discord) and start contributing too.
Thanks goes to these wonderful people ([emoji key](https://allcontributors.org/docs/en/emoji-key)):

Clément Michaud
💻 📖 🤔 🚧 💬 👀 ⚠️ 🧑🏫 🚇 🎨 📓 🔧 🔬

Amir Zarrinkafsh
💻 📖 🤔 🚧 💬 👀 ⚠️ 🧑🏫 🚇 🎨 📓 🔧 🔬

James Elliott
💻 📖 🤔 🚧 💬 👀 ⚠️ 🧑🏫 🚇 🎨 📓 🔧 🔬

Antoine Favre
🐛 🤔

BankaiNoJutsu
💻 🎨

Philipp Rintz
📖

Callan Bryant
💻 📖

Ian
💻

FrozenDragoon
💻

vdot0x23
💻

alexw1982
📖

Sohalt
💻 📖

Stoica Tedy
💻

Dylan Smith
💻

Lukas Klass
📖

Philipp Staiger
💻 📖 ⚠️

James Hodgkinson
📖

Chris Smith
📖

Mihály
📖

Silver Bullet
📖

Paul Williams
💻 ⚠️

Timo
📖

Andrew Kliskey
📖

Kristof Mattei
📖

ZMiguel Valdiviesso
📖

akusei
💻 📖

Daniel Miller
📖

Dustin Sweigart
💻 📖 ⚠️

Shawn Haggard
💻 ⚠️

Kevyn Bruyere
📖

Daniel Sutton
💻

Valentin Höbel
💻

thehedgefrog
📖

Victor
📖

Chris Whisker
📖

nasatome
📖

Begley Brothers (Development)
📖

Mike Kusold
💻

Dimitris Zervas
📖

TheCatLady
🤔

Lauri Võsandi
🤔

Kennard Vermeiren
🤔

ThinkChaos
💻 📖 ⚠️

Hasan
🛡️

David Chidell
📖

Marcel Marquardt
🐛

Ian Gallagher
📖

Wu Han
📖

lavih
📖

Jon B.
🛡️

Alex Gustafsson
💻 📖

Arsenović Arsen
💻 ⚠️ 🛡️

dakriy
💻

Dave
📓

Nicolas Reymundo
📖

polandy
📖

yossbg
💻 🎨

Michael Campbell
📖

Justin Sievenpiper
💻

Aram Akhavan
📖

Shadow
📖

Patrick Ruckstuhl
📖

Andrew Moore
💻 📖 ⚠️

Dennis Gaida
📖

Alestrix
📖

bgh-github
📖

Manuel Nuñez
💻 🌍 📖 🐛 🎨 ⚠️ 👀 🔬 🤔

protvis74
🌍

Jamie (Bear) Murphy
👀

Robin van Boven
🛡️

alphabet5
🤔

Robert Meredith
🤔

Adrian Gąsior
🛡️

James White
💬

Zhao Xiang Lim
📖

Auzborn123
🌍

SvanGlan
🌍

HannesJo0139
📖

andreas-berg
🐛

Clément Radenac
📖

boomam
📖

Northguy
📖

Brennan Kinney
📖

Michał Mieszczak
🤔 💻

Paul Ohl
📖

Stephen Kent
🤔 💻 🎨

Ohelig
📖

Dinh Bao Dang
📖

levkoburburas
💻 🤔 🐛

tiuub
📖

Josh Gordon
🤔 🛡️

silasfrancisco
🛡️

Ricardo Pesqueira
🛡️

Harold
📖

Brynn Crowley
📖 🎨

Budiman Jojo
📖

Hendrik Sievers
📖 🎨 🤔

Marcus Georgi
📖

samos667
📖

0xsysr3ll
📖

Dan
📖

Eyal Benaroche
📖

Wang Weixuan
🐛 💻 ⚠️

Dani
📖

Pierre Kisters
💻 🐛 ⚠️

Auston Pramodh Barboza
📖

Thomas Steinbach
📖

Steve-Brule
📖

peter
🐛

Nick O'Connor
🐛 📓

Nikita Pedorich
📓
This project follows the [all-contributors](https://github.com/all-contributors/all-contributors) specification.
Contributions of any kind welcome!
### Sponsors
***Help Wanted:*** We are actively looking for sponsorship to obtain either a code security audit, penetration testing,
or other audits related to improving the security of Authelia.
Any company can become a sponsor by donating or providing any benefit to the project or the team helping improve
Authelia.
#### JetBrains
Thank you to [ JetBrains](https://www.jetbrains.com/?from=Authelia)
JetBrains](https://www.jetbrains.com/?from=Authelia)
for providing us with free licenses to their great tools.
* [ IDEA](http://www.jetbrains.com/idea/)
IDEA](http://www.jetbrains.com/idea/)
* [ GoLand](http://www.jetbrains.com/go/)
GoLand](http://www.jetbrains.com/go/)
* [ WebStorm](http://www.jetbrains.com/webstorm/)
WebStorm](http://www.jetbrains.com/webstorm/)
#### Microsoft
Our pipeline agents which we rely on for productivity are hosted on [Azure](https://azure.microsoft.com/?from=Authelia)
and our [git repositories](https://github.com/authelia) are hosted on [GitHub](https://github.com/?from=Authela)
which are both [Microsoft](https://www.microsoft.com/?from=Authelia) products.
[ ](https://www.microsoft.com/?from=Authelia)
](https://www.microsoft.com/?from=Authelia)
[ ](https://azure.microsoft.com/?from=Authelia)
](https://azure.microsoft.com/?from=Authelia)
### Open Collective
#### Backers
Thank you to all our backers! 🙏 [Become a backer](https://opencollective.com/authelia-sponsors/contribute) and help us
sustain our community. The money we currently receive is dedicated to fund a security audit, and potentially in the
future introducing a bug bounty program to give us as many
eyes as we can to detect potential vulnerabilities.

#### Sponsorship
Companies contributing to Authelia via Open Collective will have a special mention below.
[Become a sponsor](https://opencollective.com/authelia-sponsors#sponsor).
## License
**Authelia** is **licensed** under the **[Apache 2.0]** license. The terms of the license are detailed in
[LICENSE](LICENSE).
[](https://app.fossa.com/projects/git%2Bgithub.com%2Fauthelia%2Fauthelia?ref=badge_large)
[Apache 2.0]: https://www.apache.org/licenses/LICENSE-2.0
[TOTP]: https://en.wikipedia.org/wiki/Time-based_One-time_Password_Algorithm
[FIDO2]: https://www.yubico.com/authentication-standards/fido2/
[YubiKey]: https://www.yubico.com/products/yubikey-5-overview/
[WebAuthn]: https://www.yubico.com/authentication-standards/webauthn/
[auth_request]: https://nginx.org/en/docs/http/ngx_http_auth_request_module.html
[config.template.yml]: ./config.template.yml
[nginx]: https://www.authelia.com/integration/proxies/nginx/
[Traefik]: https://www.authelia.com/integration/proxies/traefik/
[Caddy]: https://www.authelia.com/integration/proxies/caddy/
[Skipper]: https://www.authelia.com/integration/proxies/skipper/
[Envoy]: https://www.authelia.com/integration/proxies/envoy/
[HAProxy]: https://www.authelia.com/integration/proxies/haproxy/
[Docker]: https://docker.com/
[Kubernetes]: https://kubernetes.io/
[security]: https://github.com/authelia/authelia/security/policy
[#support]: https://discord.com/channels/707844280412012608/707844280412012612
[#contributing]: https://discord.com/channels/707844280412012608/804943261265297408
[OpenID Certified™]: https://openid.net/certification/
[OpenID Connect™ protocol]: https://openid.net/developers/how-connect-works/
