https://github.com/davidfowl/TodoApp
Todo application with ASP.NET Core Blazor WASM, Minimal APIs and Authentication
https://github.com/davidfowl/TodoApp
aspnetcore authentication blazor cookies dotnet-core jwt opentelemetry rest-api webassembly
Last synced: 10 months ago
JSON representation
Todo application with ASP.NET Core Blazor WASM, Minimal APIs and Authentication
- Host: GitHub
- URL: https://github.com/davidfowl/TodoApp
- Owner: davidfowl
- License: mit
- Created: 2021-05-04T15:37:57.000Z (about 5 years ago)
- Default Branch: main
- Last Pushed: 2025-01-11T23:44:14.000Z (over 1 year ago)
- Last Synced: 2025-07-14T06:38:54.416Z (10 months ago)
- Topics: aspnetcore, authentication, blazor, cookies, dotnet-core, jwt, opentelemetry, rest-api, webassembly
- Language: C#
- Homepage:
- Size: 1.12 MB
- Stars: 3,033
- Watchers: 74
- Forks: 449
- Open Issues: 4
-
Metadata Files:
- Readme: README.md
- License: LICENSE
Awesome Lists containing this project
README
## Todo application with ASP.NET Core
[](https://github.com/davidfowl/TodoApi/actions/workflows/ci.yaml)
This is a Todo application that features:
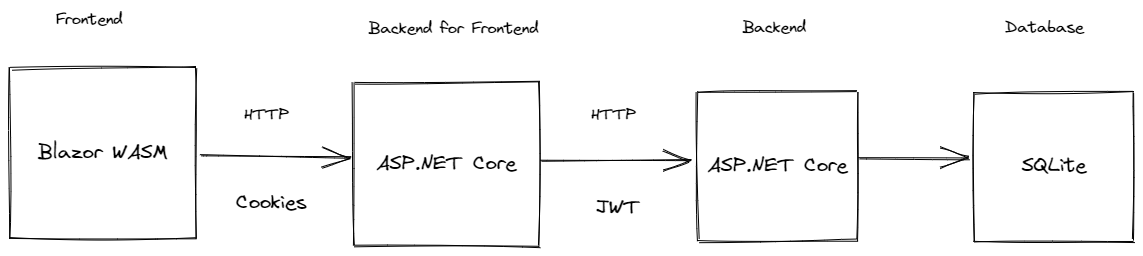
- [**Todo.Web**](Todo.Web) - An ASP.NET Core hosted Blazor WASM front end application
- [**Todo.Api**](Todo.Api) - An ASP.NET Core REST API backend using minimal APIs
It showcases:
- Blazor WebAssembly
- Minimal APIs
- Using EntityFramework and SQLite for data access
- OpenAPI
- User management with ASP.NET Core Identity
- Cookie authentication
- Bearer authentication
- Proxying requests from the front end application server using YARP's IHttpForwarder
- Rate Limiting
- Writing integration tests for your REST API
## Prerequisites
### .NET
1. [Install .NET 9](https://dotnet.microsoft.com/en-us/download/dotnet/9.0)
### Database
The application uses SQLite and entity framework. .NET Aspire is used to bootstrap all dependencies.
### Running the application
To run the application, run the [TodoApp.AppHost](TodoApp.AppHost) project. This uses .NET Aspire to run both the [Todo.Web/Server](Todo.Web/Server) and [Todo.Api](Todo.Api).
## Optional
### Using the API standalone
The Todo REST API can run standalone as well. You can run the [Todo.Api](Todo.Api) project and make requests to various endpoints using the Swagger UI (or a client of your choice):

Before executing any requests, you need to create a user and get an auth token.
1. To create a new user, run the application and POST a JSON payload to `/users/register` endpoint:
```json
{
"email": "myuser@contoso.com",
"password": ""
}
```
1. To get a token for the above user, hit the `/users/login` endpoint with the above user email and password. The response will look like this:
```json
{
"tokenType": "Bearer",
"accessToken": "string",
"expiresIn": ,
"refreshToken": "string"
}
```
1. You should be able to use the accessToken to make authenticated requests to the todo endpoints.
### Social authentication
In addition to username and password, social authentication providers can be configured to work with this todo application. By default
it supports Github, Google, and Microsoft accounts.
Instructions for setting up each of these providers can be found at:
- [Github](https://docs.github.com/en/developers/apps/building-oauth-apps)
- [Microsoft](https://learn.microsoft.com/en-us/aspnet/core/security/authentication/social/microsoft-logins)
- [Google](https://learn.microsoft.com/en-us/aspnet/core/security/authentication/social/google-logins)
Once you obtain the client id and client secret, the configuration for these providers must be added with the following schema:
```JSON
{
"Authentication": {
"Schemes": {
"": {
"ClientId": "xxx",
"ClientSecret": "xxxx"
}
}
}
}
```
Or using environment variables:
```
Authentication__Schemes____ClientId=xxx
Authentication__Schemes____ClientSecret=xxx
```
Or using user secrets:
```
dotnet user-secrets set Authentication:Schemes::ClientId xxx
dotnet user-secrets set Authentication:Schemes::ClientSecret xxx
```
Other providers can be found [here](https://github.com/aspnet-contrib/AspNet.Security.OAuth.Providers#providers).
These must be added to [AuthenticationExtensions](Todo.Web/Server/Authentication/AuthenticationExtensions.cs) as well.
**NOTE: Don't store client secrets in configuration!**
#### Auth0
This sample has **Auth0** configured as an OIDC server. It can be configured with the following schema:
```JSON
{
"Authentication": {
"Schemes": {
"Auth0": {
"Audience": "",
"Domain": "",
"ClientId": "",
"ClientSecret": ""
}
}
}
}
```
Learn more about the Auth0 .NET SDK [here](https://github.com/auth0/auth0-aspnetcore-authentication).
### OpenTelemetry
This app uses OpenTelemetry to collect logs, metrics and spans. You can see this
using the [Aspire Dashboard](https://aspiredashboard.com/).