https://github.com/enemy-submarine/pidrila
Python Interactive Deepweb-oriented Rapid Intelligent Link Analyzer
https://github.com/enemy-submarine/pidrila
appsec bug-bounty dirbuster hacking netstalking penetration-testing pentest pentesting python scanner scanner-web security
Last synced: about 1 year ago
JSON representation
Python Interactive Deepweb-oriented Rapid Intelligent Link Analyzer
- Host: GitHub
- URL: https://github.com/enemy-submarine/pidrila
- Owner: enemy-submarine
- License: gpl-2.0
- Created: 2020-11-08T18:52:07.000Z (over 5 years ago)
- Default Branch: main
- Last Pushed: 2020-11-08T19:14:12.000Z (over 5 years ago)
- Last Synced: 2024-08-01T19:44:17.407Z (almost 2 years ago)
- Topics: appsec, bug-bounty, dirbuster, hacking, netstalking, penetration-testing, pentest, pentesting, python, scanner, scanner-web, security
- Language: Python
- Homepage:
- Size: 135 KB
- Stars: 203
- Watchers: 10
- Forks: 29
- Open Issues: 7
-
Metadata Files:
- Readme: README.md
- License: LICENSE
Awesome Lists containing this project
- osint_stuff_tool_collection - Pidrila - oriented Rapid Intelligent Link Analyzer | ([](#table-of-contents) Table of contents / [](#website-analyze)Website analyze)
- awesome-hacking-lists - enemy-submarine/pidrila - Python Interactive Deepweb-oriented Rapid Intelligent Link Analyzer (Python)
README
PIDRILA
=========
Current Release: v0.1.0 (2020.11.08)
Overview
--------
**PIDRILA**: **P**ython **I**nteractive **D**eepweb-oriented **R**apid **I**ntelligent **L**ink **A**nalyzer is really fast async web path scanner prototype
developed by BrightSearch team for all ethical netstalkers.
Installation & Usage
------------
```
git clone https://github.com/enemy-submarine/pidrila.git
cd pidrila
python3 pidrila.py -u
```
Options
-------
```
Usage: pidrila.py [OPTIONS]
Options:
-U, --user-agent TEXT User-Agent
-t, --timeout INTEGER Request timeout [default: 30]
-A, --auth TEXT Basic HTTP auth, i.e. login:password
-M, --max-connections-per-host INTEGER
How many simultaneous connections should we
open (per each host) [default: 16]
-m, --max-connections INTEGER How many simultaneous connections should we
open [default: 128]
-p, --proxy TEXT Proxy address, like socks5h://127.0.0.1:9050
-p, --pathlist FILENAME Path list
-L, --url-list FILENAME Target URL list
-u, --url TEXT Target URL, option is mutually exclusive
with url_list [required]
-l, --logs DIRECTORY Destination directory for the logs
--http-method [head|get] HTTP method: GET or HEAD [default: get]
--help Show this message and exit.
```
Features
--------
- Asynchronous
- Can simultaneously scan unlimited number of sites
- Keep-alive support
- HTTP and SOCKS proxy support
- User agent randomization
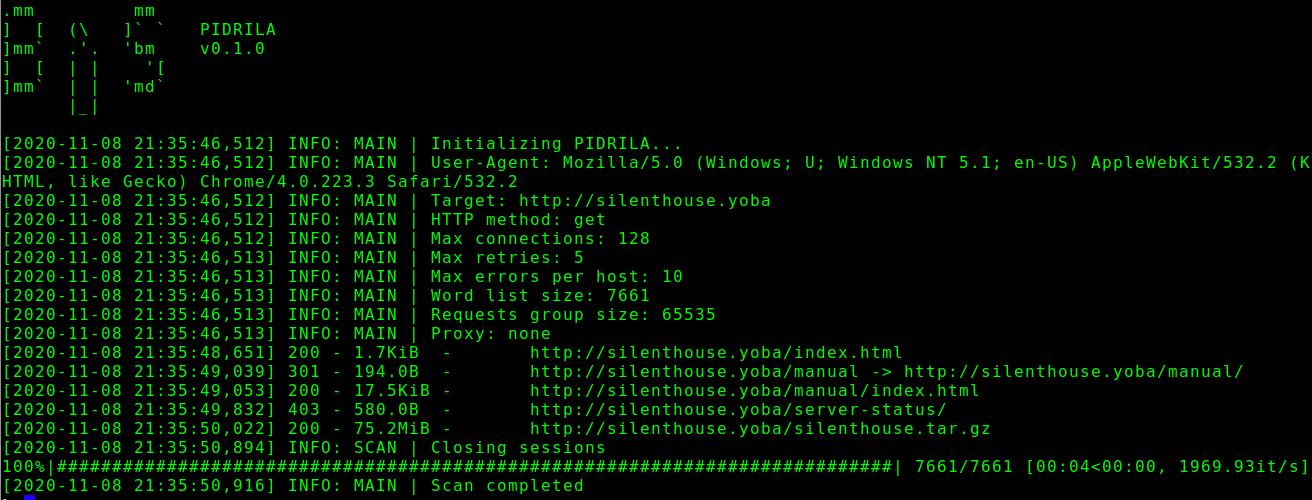
Screenshot
--------
Usage examples
--------
Scan single clearweb site
```
python3 ./pidrila.py -u http://silenthouse.yoba -M 128
```
Scan single onion site
```
python3 ./pidrila.py -u http://zqktlwi4fecvo6ro.onion -m 16 -M 16 --proxy=socks5h://127.0.0.1:9050
```
Fast batch scan with custom User-Agent
```
python3 ./pidrila.py -m 2048 -L darkweb_sites_list.txt --user-agent "Pantusha/2.0 (4.2BSD)"
```
License
-------
License: GNU General Public License, version 2