https://github.com/qeeqbox/authentication-bypass
A threat actor may gain access to data and functionalities by bypassing the target authentication mechanism
https://github.com/qeeqbox/authentication-bypass
authentication bypass example infosecsimplified metadata qeeqbox visualization vulnerability
Last synced: about 1 month ago
JSON representation
A threat actor may gain access to data and functionalities by bypassing the target authentication mechanism
- Host: GitHub
- URL: https://github.com/qeeqbox/authentication-bypass
- Owner: qeeqbox
- License: agpl-3.0
- Created: 2022-04-20T20:43:51.000Z (about 4 years ago)
- Default Branch: main
- Last Pushed: 2025-08-24T19:12:54.000Z (8 months ago)
- Last Synced: 2025-08-24T23:21:46.684Z (8 months ago)
- Topics: authentication, bypass, example, infosecsimplified, metadata, qeeqbox, visualization, vulnerability
- Homepage:
- Size: 2.08 MB
- Stars: 2
- Watchers: 1
- Forks: 0
- Open Issues: 0
-
Metadata Files:
- Readme: README.md
- License: LICENSE
Awesome Lists containing this project
README

A threat actor is able to bypass the access controllers and gain access to the target
Clone this current repo recursively
```sh
git clone --recurse-submodules httbypassps://github.com/qeeqbox/authentication-
```
Run the webapp using Python
```sh
python3 authentication-bypass/vulnerable-web-app/webapp.py
```
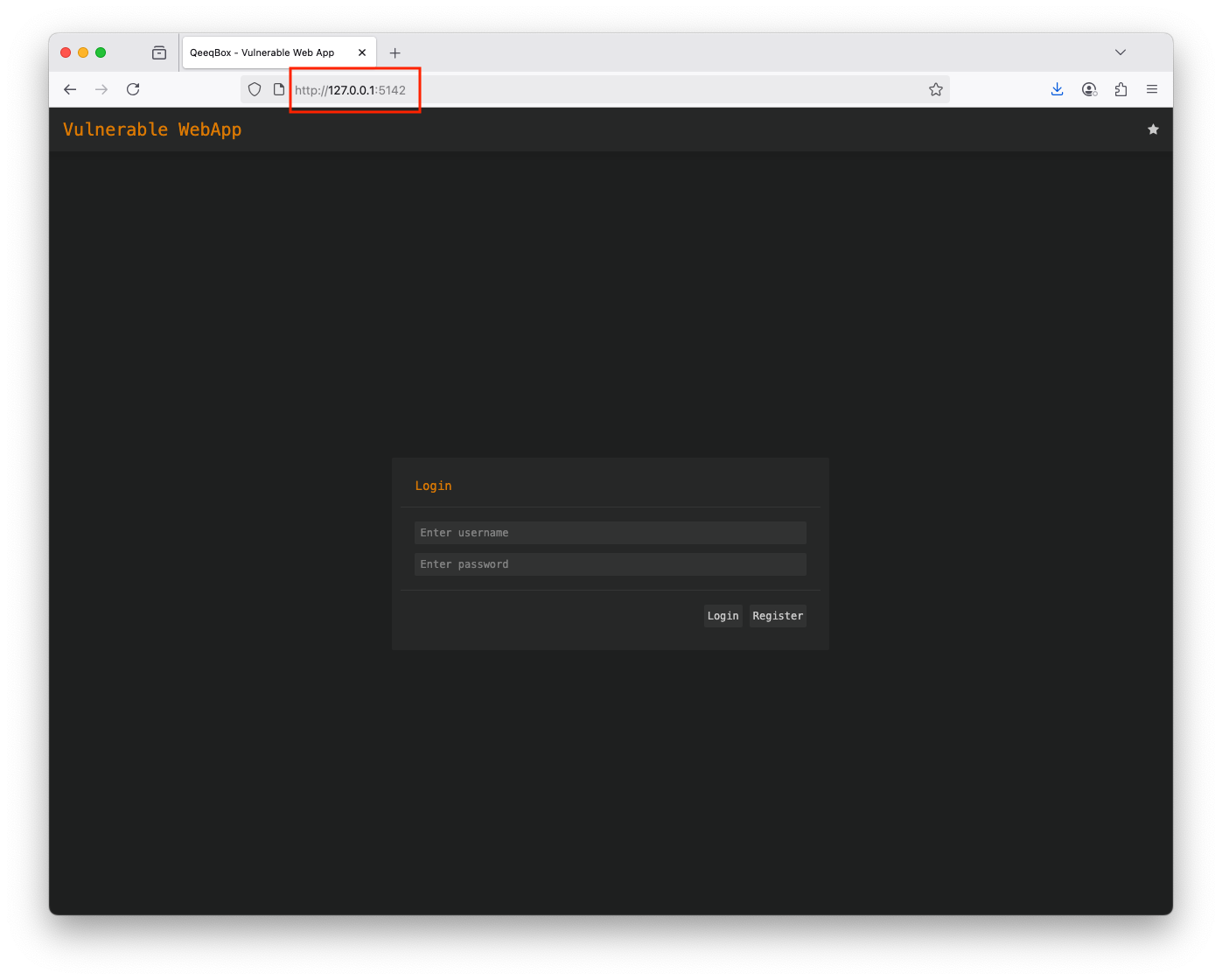
Open the webapp in your browser 127.0.0.1:5142
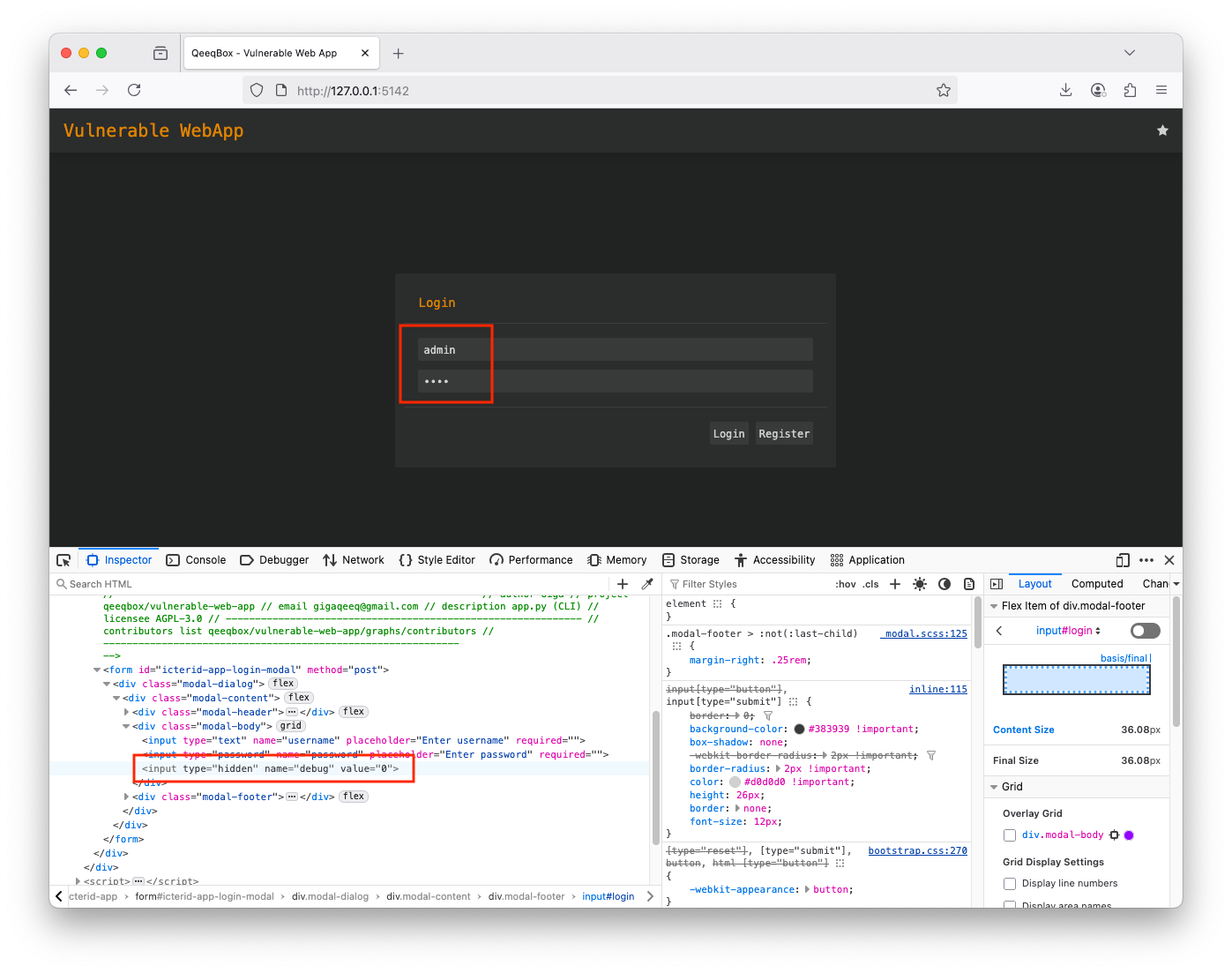
Right-click on the page and open Developer Tools, find the hidden variable named debug in the post form
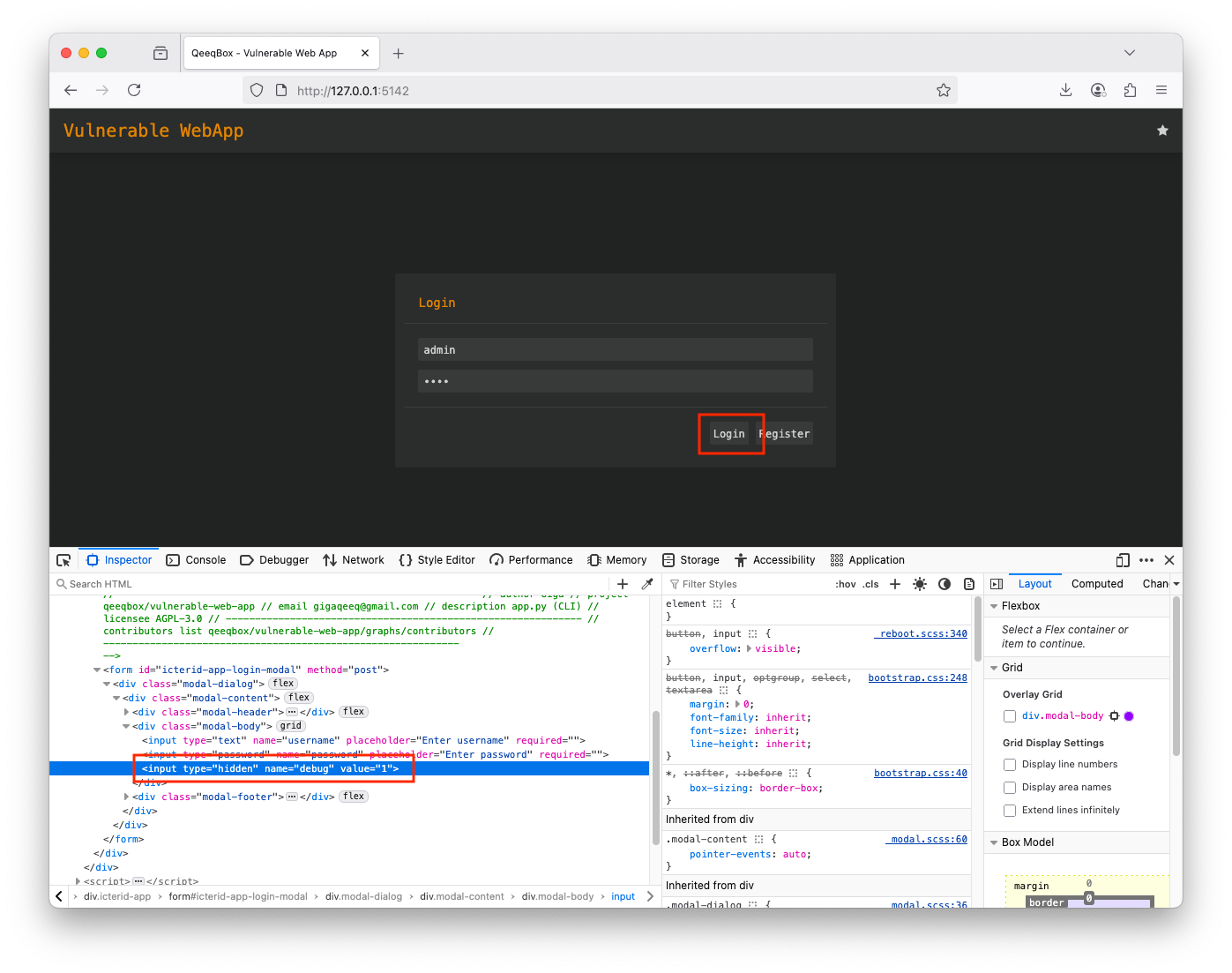
Change the variable debug from 0 to 1, this hit log in
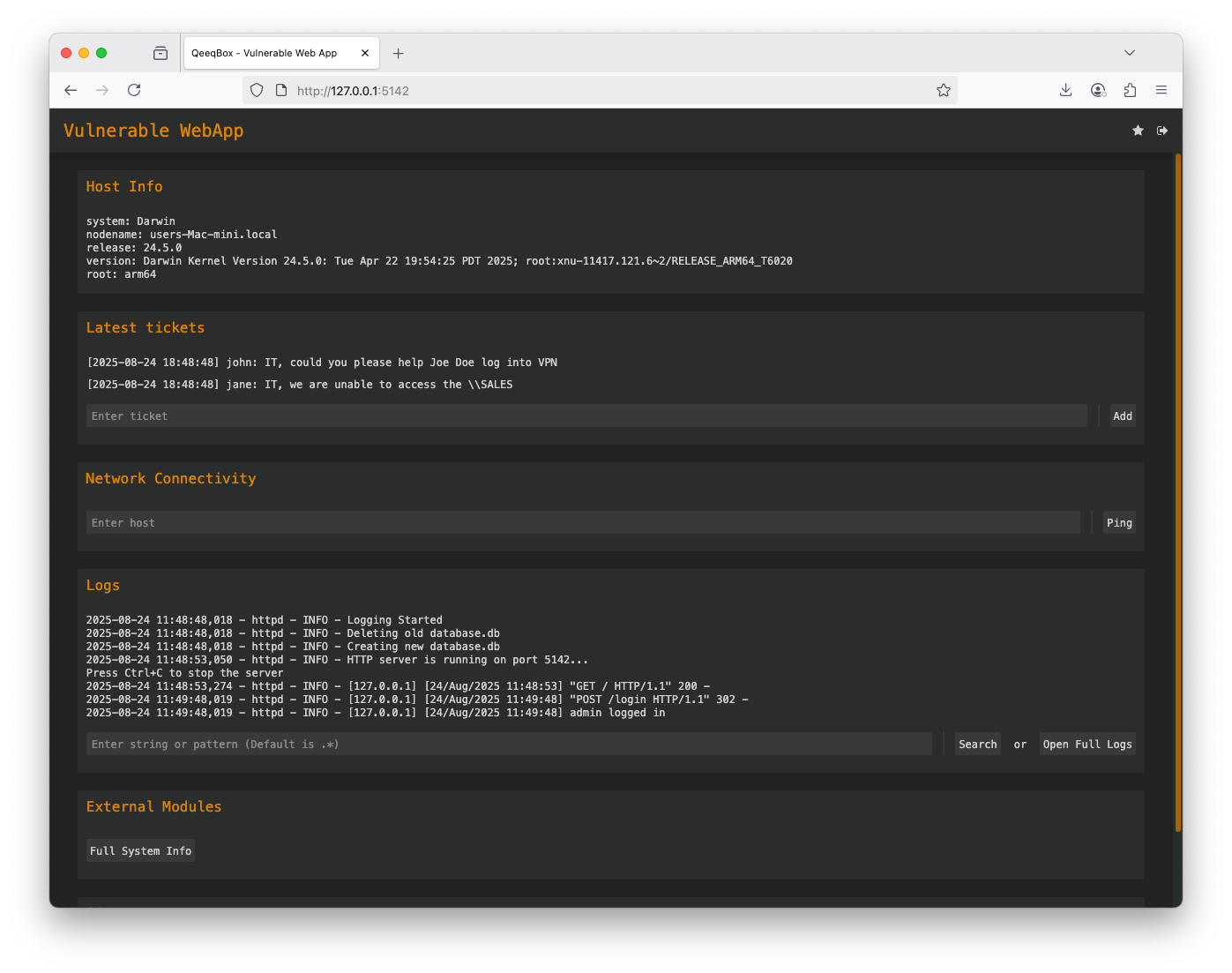
You are logged as admin
## Code
When a user logs in using a username and password in POST request to the login route, a hidden variable called debug is checked, if it's 1, the
```py
if parsed_url.path == "/login" and "username" in post_request_data and "password" in post_request_data:
ret = self.check_creds(post_request_data['username'][0],post_request_data['password'][0])
if isinstance(ret, list) and ret[0] == "valid":
self.send_content(302, self.gen_cookie(ret[1],60*15)+[('Location', URL)], None)
self.log_message("%s logged in" % post_request_data['username'][0])
return
elif isinstance(ret, list) and ret[0] == "password":
if "debug" in post_request_data:
if post_request_data["debug"][0] == "1":
self.send_content(302, self.gen_cookie(ret[1],60*15)+[('Location', URL)], None)
self.log_message("%s logged in" % post_request_data['username'][0])
return
self.send_content(401, [('Content-type', 'text/html')], self.msg_page(f"Password is wrong".encode("utf-8"), b"login"))
return
elif isinstance(ret, list) and ret[0] == "username" or isinstance(ret, list) and ret[0] == "error":
self.send_content(401, [('Content-type', 'text/html')], self.msg_page(f"User {post_request_data['username'][0]} doesn't exist".encode("utf-8"), b"login"))
return
```