https://github.com/qeeqbox/default-credential
A threat actor may gain unauthorized access using the default username and password
https://github.com/qeeqbox/default-credential
credentials default example infosecsimplified metadata qeeqbox visualization vulnerability
Last synced: about 1 month ago
JSON representation
A threat actor may gain unauthorized access using the default username and password
- Host: GitHub
- URL: https://github.com/qeeqbox/default-credential
- Owner: qeeqbox
- License: agpl-3.0
- Created: 2022-04-20T20:42:13.000Z (about 4 years ago)
- Default Branch: main
- Last Pushed: 2025-07-26T21:10:26.000Z (9 months ago)
- Last Synced: 2025-07-27T01:11:54.943Z (9 months ago)
- Topics: credentials, default, example, infosecsimplified, metadata, qeeqbox, visualization, vulnerability
- Homepage:
- Size: 1.21 MB
- Stars: 2
- Watchers: 1
- Forks: 0
- Open Issues: 0
-
Metadata Files:
- Readme: README.md
- License: LICENSE
Awesome Lists containing this project
README

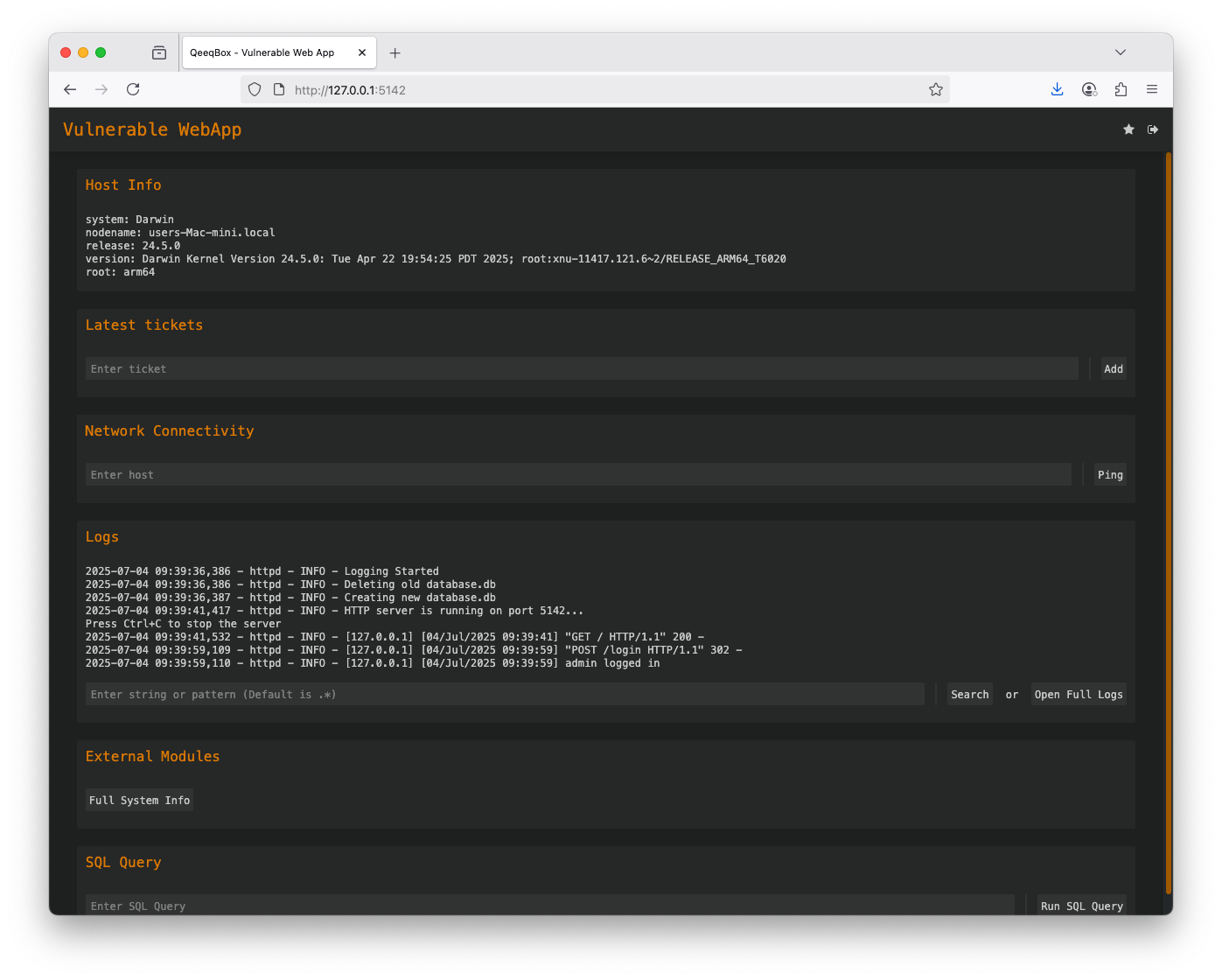
Manufacturers or developers typically set default credentials, such as username and password combinations, for devices, software, and systems. These credentials are intended for initial access. A threat actor may exploit default credentials to gain unauthorized access to the system or data.
## Example
Clone this current repo recursively
```sh
git clone --recurse-submodules https://github.com/qeeqbox/default-credential
```
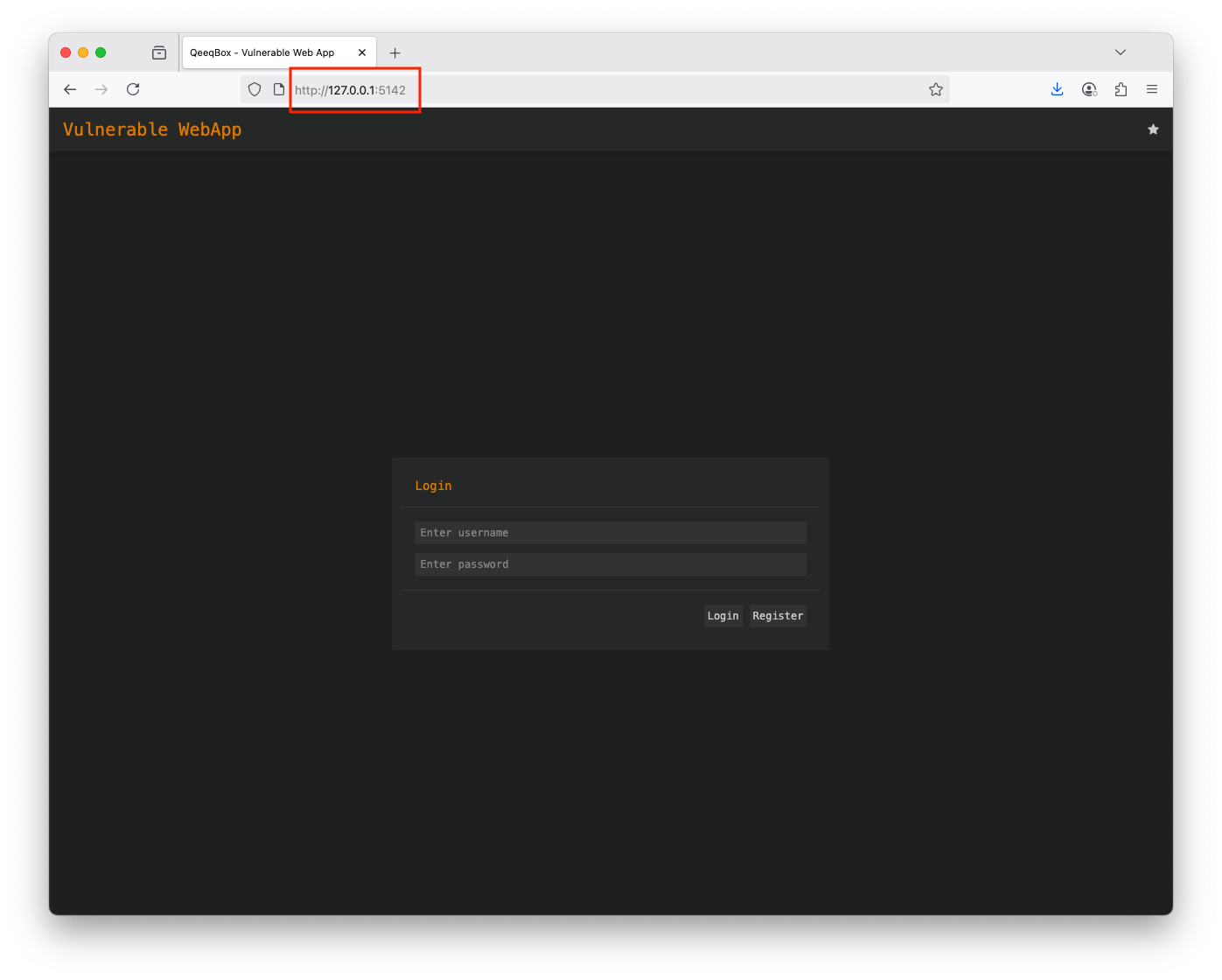
Run the webapp using Python
```sh
python3 default-credential/vulnerable-web-app/webapp.py
```
Open the webapp in your browser 127.0.0.1:5142
Use the default credentials (username: admin and password: admin) to login
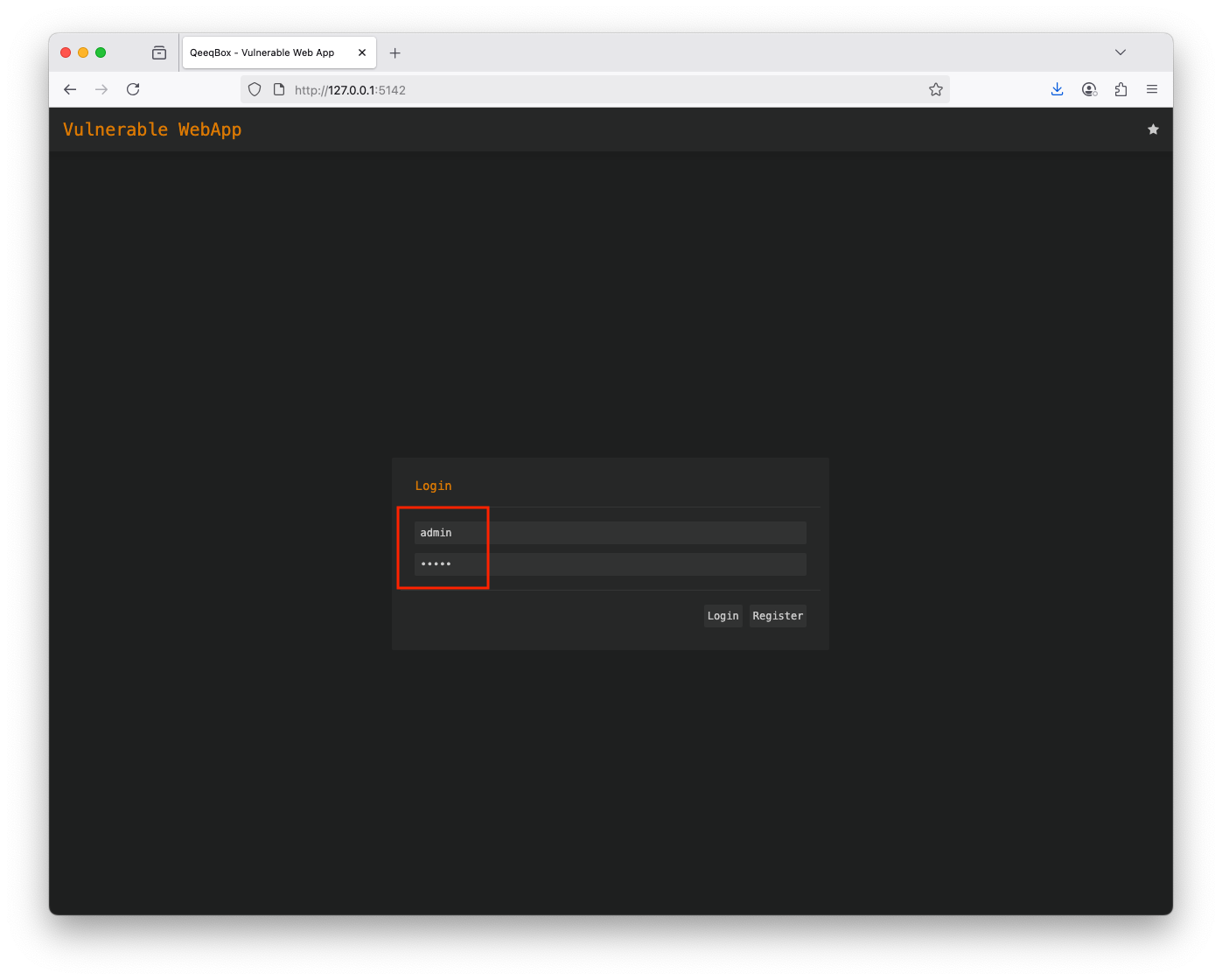
You have full control over the web app interface