https://github.com/sbousseaden/evtx-attack-samples
Windows Events Attack Samples
https://github.com/sbousseaden/evtx-attack-samples
dataset detection-engineering dfir evtx mitre-attack threat-hunting windows-security winlogbeat
Last synced: 12 months ago
JSON representation
Windows Events Attack Samples
- Host: GitHub
- URL: https://github.com/sbousseaden/evtx-attack-samples
- Owner: sbousseaden
- License: gpl-3.0
- Created: 2019-03-15T08:45:44.000Z (almost 7 years ago)
- Default Branch: master
- Last Pushed: 2023-01-24T12:02:51.000Z (about 3 years ago)
- Last Synced: 2024-10-26T07:39:25.505Z (over 1 year ago)
- Topics: dataset, detection-engineering, dfir, evtx, mitre-attack, threat-hunting, windows-security, winlogbeat
- Language: HTML
- Homepage: https://github.com/sbousseaden/EVTX-ATTACK-SAMPLES
- Size: 6.05 MB
- Stars: 2,233
- Watchers: 144
- Forks: 399
- Open Issues: 5
-
Metadata Files:
- Readme: README.md
- License: LICENSE.GPL
Awesome Lists containing this project
- awesome-reverse-engineering - **609**星
README
# Windows EVTX Samples [200 EVTX examples]:
This is a container for windows events samples associated to specific attack and post-exploitation techniques.
Can be useful for:
- Testing your detection scripts based on EVTX parsing
- Training on DFIR and threat hunting using event logs
- Designing detection use cases using Windows and Sysmon event logs
- Avoid/Bypass the noisy techniques if you are a redteamer
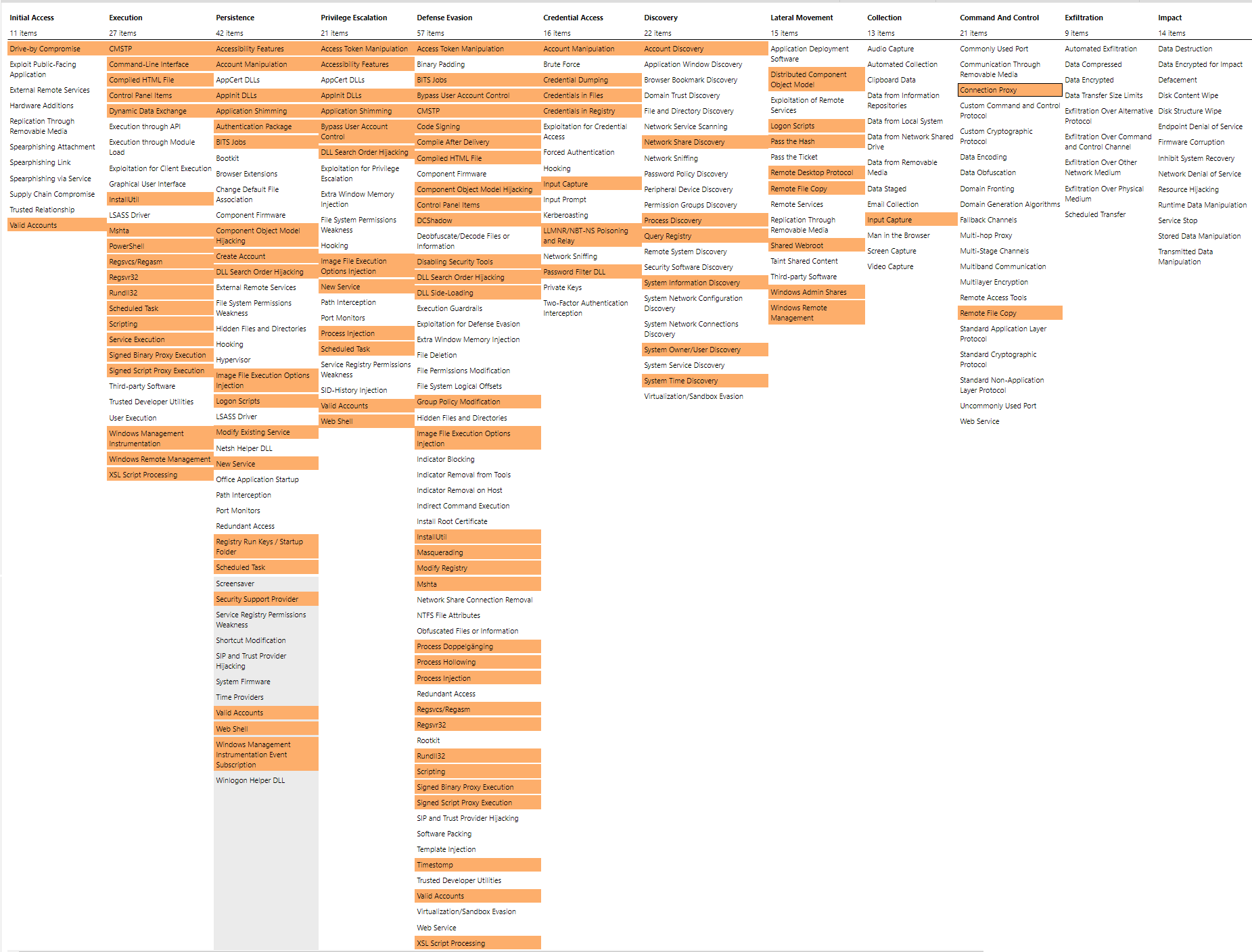
N.B: Mapping has been done to the level of ATT&CK technique (not procedure).
Details of the EVTX content mapped to MITRE tactics can be found [here](http://bit.ly/2WpzQM4), stats summary:


Overview of the covered TTPs using attack-navigator:
# Winlogbeat-Bulk-Read
Included is a PowerShell script that can loop through, parse, and replay evtx files with [winlogbeat](https://www.elastic.co/downloads/beats/winlogbeat).
This can be useful to replay logs into an ELK stack or to a local file. By default this script will
output logs to .\winlogbeat\events.json as configured in the winlogbeat_example.yml file,
you can configure any of your own destinations in winlogbeat.yml (excluded from git) and the
example config file will be ignored if winlogbeat.yml is found.
Winlogbeat-Bulk-Read Usage:
```
## Display help along with examples:
.\Winlogbeat-Bulk-Read.ps1 -Help
## Run with defaults (read ./ recursively and look for winlogbeat.exe in your path):
.\Winlogbeat-Bulk-Read.ps1
## If you want to point this script at another directory with evtx files and specify a path to the winlogbeat.exe binary:
.\Winlogbeat-Bulk-Read.ps1 -Exe ~\Downloads\winlogbeat\winlogbeat.exe -Source "..\EVTX-ATTACK-SAMPLES\"
```
# License:
EVTX_ATT&CK's [GNU General Public License](https://github.com/sbousseaden/EVTX-ATTACK-SAMPLES/blob/master/LICENSE.GPL)