https://github.com/swisskyrepo/DamnWebScanner
Another web vulnerabilities scanner, this extension works on Chrome and Opera
https://github.com/swisskyrepo/DamnWebScanner
extension lfi plugin polyglot-vector rce scans sql-injection web-vulnerabilities-scanner webbrowser xss-vulnerability
Last synced: 5 months ago
JSON representation
Another web vulnerabilities scanner, this extension works on Chrome and Opera
- Host: GitHub
- URL: https://github.com/swisskyrepo/DamnWebScanner
- Owner: swisskyrepo
- Created: 2016-12-24T16:41:24.000Z (almost 9 years ago)
- Default Branch: master
- Last Pushed: 2019-09-22T14:11:50.000Z (about 6 years ago)
- Last Synced: 2025-05-25T13:05:24.712Z (7 months ago)
- Topics: extension, lfi, plugin, polyglot-vector, rce, scans, sql-injection, web-vulnerabilities-scanner, webbrowser, xss-vulnerability
- Language: Python
- Size: 1.37 MB
- Stars: 458
- Watchers: 17
- Forks: 158
- Open Issues: 1
-
Metadata Files:
- Readme: README.md
- Funding: .github/FUNDING.yml
Awesome Lists containing this project
- awesome-hacking-lists - swisskyrepo/DamnWebScanner - Another web vulnerabilities scanner, this extension works on Chrome and Opera (Python)
README
# Damn Web Scanner
Another web vulnerabilities scanner, this extension works on Chrome and Opera.
The extension is working on the background and will notify you if it finds any vulnerability.
Currently it scans for:
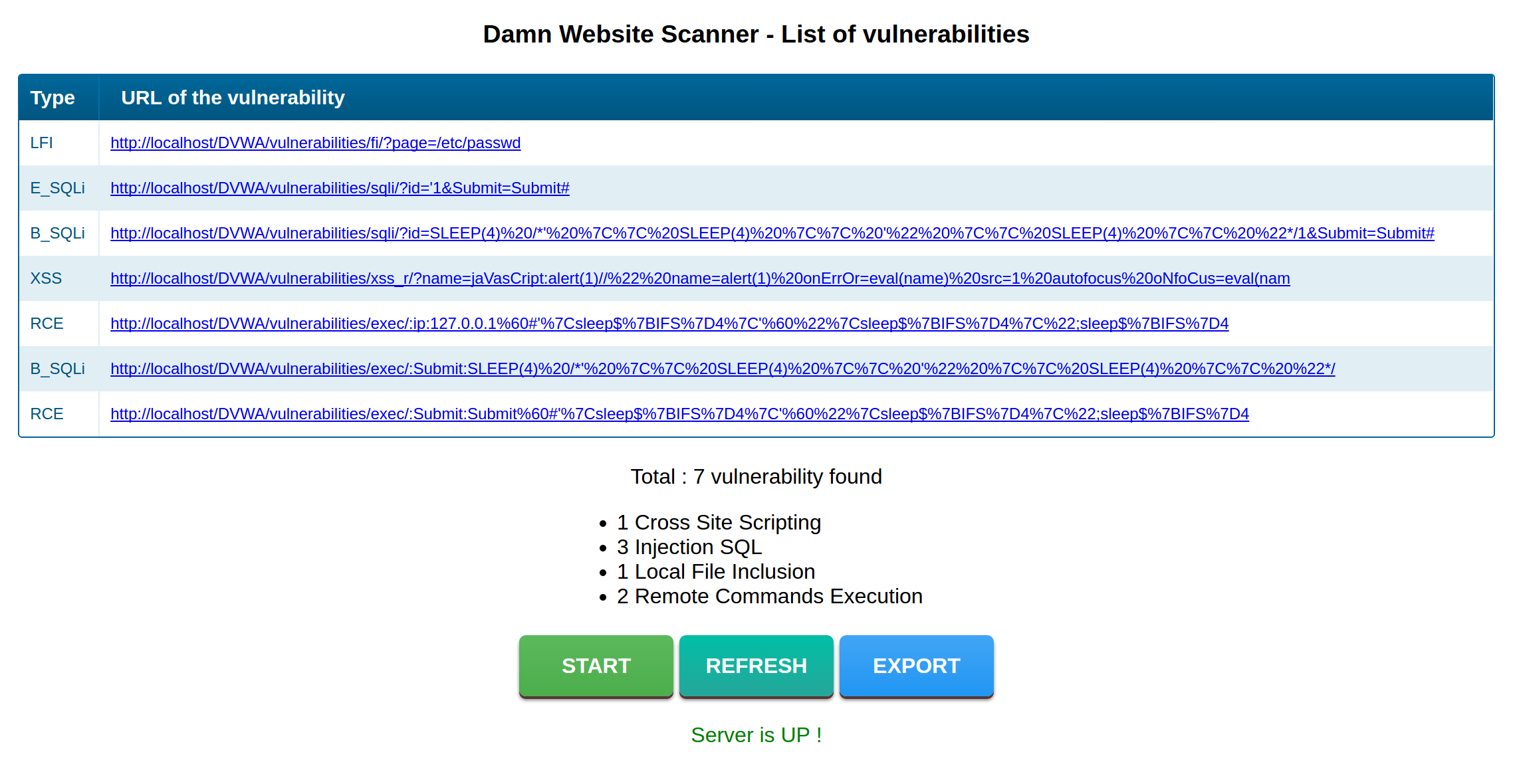
- SQL Injection : Time based SQLi scanner using polyglot vectors (MySQL, SQLite, Oracle, Postgresql, SQL Server)
- Cross Site Scripting : Using a browser simulator (Ghost)
- Local File Inclusion
- Remote Commands Execution using polyglot vectors based on time
All the features are:
- Detect if the server is up with a "/ping" request
- New XSS vectors, work in different contexts (JS var, JS function, inside HTML tag, outside HTML tag)
- Basic page to list the vulnerabilities URL and TYPE
- Re-use your cookies and user-agent to get access to page with cookie-authentication
- Export vulnerabilities into a CSV file
- Launch scan when a form is submitted or a page is opened via the URL bar
**Warning :** Do not use this extension for illegal purpose, the main goal of it is to simplify the life of bug hunters. It's a **BETA version**, many improvements will come don't worry
**Warning :** A crash can happen server-side, this issue isn't resolved yet. The docker-compose.yml is set to automatically restart the docker when this happen..
## Install
You need to install and configure the server, it uses ghost and flask.
1. To get started you only need to start the docker and the dependencies will be installed.
```bash
cd server
sudo docker-compose -f docker-compose.yml up -d --build
```
2. Edit the server configuration
By default it's listening to the port 8000, it can be modified in the following files : popup.js, background.js, docker-compose.yml
```js
var config_server = "http://127.0.0.1:8000";
```
3. The extension isn't packed, to use it go to chrome://extensions or opera://extensions then select "Load unpacked extension"
4. Browse the internet ! (Don't forget to start the extension by clicking the 'START' button)
You can try the Error SQL, Blind SQL, LFI with Damn Vulnerable Web App.
The SQL Injection scanner was also tested on https://pentesterlab.com/badges/essential.
## Debugging
It's strongly recommended to debug any problem with Portainer using the logs table.
```
http://127.0.0.1:9000/#/containers/[INSERT HERE THE CONTAINER'S ID]/logs
```
You will have an output like this :
```
STDOUT
---[ POST - New parameter rememberme for url: http://[REDACTED]/login.php ]---
[94mXSS Failed [0m for rememberme with the payload : jaVasCript:alert(1)//" name=alert(1) ]'">